What is Blockchain Consensus Mechanisms?
Upon first encountering blockchain technology, one fundamental question immediately springs to mind: how can a global network of hundreds of thousands of participants establish trust without any central authority? The answer lies in consensus mechanisms—a set of protocols and procedures that enable distributed agreement on updates to the ledger. In this article, we’ll explore the most prevalent consensus algorithms—from Proof of Work and Proof of Stake to various hybrid models—assessing their strengths, weaknesses, and real-world applications across different blockchain projects.
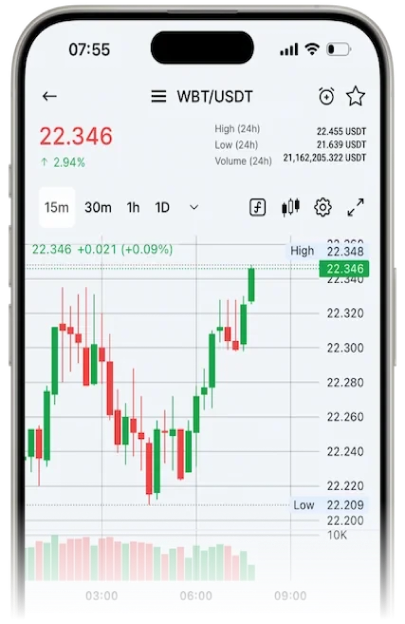
Trade crypto on WhiteBIT
What is Consensus Algorithm?
Consensus mechanism is a set of algorithms and protocols that allow every node in a distributed network to agree on the order, authenticity, and permanence of entries in a shared ledger. By verifying and finalizing transactions without the need for a central authority, blockchain consensus protects against double-spending and network attacks, ensuring that each new block is added only after it receives sufficient approval from participants, in line with the protocol’s rules.
Key Objectives of Consensus Algorithms
Blockchain consensus grapples with three interdependent—and often competing—goals: security, decentralization, and scalability. This “blockchain trilemma” highlights that bolstering security via steep economic or computational barriers, broadening node participation to eliminate single points of failure, and processing high transaction volumes with minimal latency can’t all be maximized simultaneously. Consequently, each algorithm blockchain represents a unique compromise among these three dimensions.
- Security: hinges on erecting economic or computational hurdles to potential attackers. In Proof of Work, security derives from the immense energy expenditure required to mine blocks; in Proof of Stake, it comes from locking up tokens as collateral. The steeper the cost to mount an attack—be that forging blocks or double-spending—the more resilient the network becomes against threats like a 51% attack.

- Decentralization is achieved by dispersing consensus across a large and diverse set of nodes, thereby removing single points of failure and reducing censorship risk. However, as node counts climb, transaction confirmation slows and network bandwidth demands escalate, challenging overall performance.
- Scalability: focuses on handling a high throughput of transactions at low cost and latency. Solutions often involve limiting the number of validators in the main network or offloading work to Layer 2 protocols and sharding. While these approaches can dramatically boost capacity, they may introduce additional complexity to the security model or dilute decentralization.
Before delving into specific consensus mechanisms across different network types, it’s helpful to distinguish between the models underpinning permissioned and permissionless blockchains.
Public and Private Blockchains
In permissionless (public) blockchains, anyone can join, contribute to block production, and earn rewards, so probabilistic consensus reigns supreme. In Proof of Work, for instance, miners compete to solve cryptographic puzzles, and their probability of mining the next block is proportional to their hash power. A block only becomes “final” after several confirmations—typically six to twelve additional blocks—mitigating fork risks but introducing finality delays and a slim possibility of rollbacks.
By contrast, permissioned (private) networks restrict validator membership—often to a consortium of banks or enterprises—and can therefore employ deterministic protocols such as Practical Byzantine Fault Tolerance (PBFT) or Raft. Validators exchange messages and cast votes on each proposed block; once a supermajority (usually two-thirds plus one) is reached, the block is irrevocably committed. This approach delivers instant finality and high throughput but relies on trust in the pre-approved validator set.
Classic algorithms for Public Networks
The most common among public blockchain networks are Proof-of-Work and Proof-of-Stake. Let’s take a look at each of them.
Proof-of-Work (PoW)
Proof-of-Work is the pioneering algorithm for blockchain first introduced by Bitcoin. In PoW, miners race to solve a cryptographic “puzzle”: they iterate over a special value (the nonce) such that, when combined with the candidate block’s contents and the previous block’s hash, the resulting hash falls below a dynamically adjusted target. This proof of computational effort deters abuse—altering a block would require redoing the work for that block and every subsequent one. The network calibrates difficulty so that, on average, a new block is found every ten minutes, maintaining a steady issuance rate and predictable security economics.
The PoW consensus crypto works as follows:
Assemble a Block Candidate. A node gathers pending transactions, bundles them into a new block, and appends metadata—including the previous block’s hash and its height.
↓
Search for the Valid Nonce. The miner iteratively tests different nonce values, hashing the entire block each time and checking whether the result falls below the current difficulty target. Higher difficulty means more hash attempts are needed to find a “small enough” value.
↓
Validate and Propagate. Once the miner discovers a valid nonce, they broadcast the block to the network. Peers verify the block’s hash and ensure none of the included transactions have been tampered with.
↓
Claim the Reward. The successful miner earns freshly minted coins plus the transaction fees contained in the block.
PoW Pros:
- Robust security: Executing a 51% attack requires controlling a majority of the network’s total hash power—an economically and technically prohibitive feat on large-scale blockchains.
- Proven reliability: Having safeguarded Bitcoin and other networks for over a decade, PoW’s resilience against diverse attack vectors is well established.
- Open participation: At inception, anyone with a standard computer could join the mining process without prior authorization, fostering initial decentralization.
PoW Cons:
- High energy consumption: Escalating difficulty drives up electricity usage dramatically, raising both environmental and cost concerns.
- Limited throughput and latency: Transaction processing remains comparatively slow, with finality delays often ranging from 10 to 60 minutes.
- Mining centralization: Economies of scale incentivize miners to coalesce into pools and deploy specialized hardware farms, which can erode true decentralization.
Examples of PoW cryptocurrencies: Bitcoin (BTC), Litecoin (LTC), Monero (XMR), Zcash (ZEC), Dogecoin (DOGE).

Proof-of-Stake
Proof-of-Stake awards block‐proposal rights based on the number of tokens a participant locks up in a smart contract: the larger your *stake, the greater your chance of being chosen as a validator. To curb the influence of whales, most PoS systems layer in randomness—often via a Verifiable Random Function (VRF)—and introduce factors like stake age, validator commission, or reputation. Once a validator creates a block, peers verify its transactions—and any malicious behavior can trigger slashing penalties, forfeiting part of the offender’s stake. By eliminating energy-intensive mining, PoS slashes power consumption and delivers near-instant finality compared with traditional PoW.
*Staking: the act of locking cryptocurrency in a PoS network to secure the chain and earn rewards.
The PoS consensus mechanism works as follows:
Validator Pool Formation. Participants lock tokens into a staking smart contract, earning validator status in return.
↓
Validator selection: the protocol randomly selects one or more validators from the pool, considering their stake and incorporating unpredictability factors (such as VRF).
↓
Block proposal: The selected validator gathers unconfirmed transactions, constructs a new block, and submits it to the network.
↓
Voting and finalization: The other validators “vote” with their staked tokens to confirm the block’s validity. Once a quorum (usually ≥ two-thirds) is reached, the block is finalized.
↓
Rewards and penalties: Honest validators receive rewards, typically a commission and newly issued tokens, while malicious actions, such as double-signing, incur penalties like slashing.
Pros of PoS:
- Energy efficiency: By eliminating the need for resource-heavy mining, PoS drastically cuts electricity consumption and hardware costs.
- High throughput and rapid finality: Transactions are confirmed in seconds, and block finalization is almost instantaneous, enabling a more responsive network.
- Economic deterrence: The risk of losing staked tokens incentivizes validators to act honestly, making attacks financially costly.
Cons of PoS:
- Staking centralization: Large token holders can consolidate influence, leading to disproportionate rewards and reducing true decentralization.
- The “nothing at stake” problem: Without adequate penalties, validators could theoretically support multiple chains, requiring additional mechanisms to prevent this issue.
- Protocol complexity: Properly implementing slashing and failure protection requires sophisticated algorithms and extensive testing to ensure reliability and security.
Examples of PoS cryptocurrencies: Ethereum (ETH), Cardano (ADA), Polkadot (DOT), Algorand (ALGO).
The Difference Between Proof of Stake and Proof of Work (POS vs POW)
Read the articleEvolution and Variations of PoS
As the blockchain ecosystem has matured, the traditional Proof-of-Stake (PoS) model has seen various adaptations and protocol “forks” designed to enhance performance, security, and flexibility in governance. Below, we explore the main areas of PoS evolution.
Delegated Proof-of-Stake (DPoS)
DPoS is a consensus mechanism in blockchain that blends the benefits of decentralization with high throughput. Token holders vote (1 token = 1 vote) to elect a limited group of “witnesses” (validators) who are tasked with transaction verification and block creation. The top N witnesses receive compensation for their work and can be swiftly replaced if they fail to meet performance standards, promoting both reliability and efficiency. Additionally, delegates are chosen to propose and implement major protocol changes. This structure enables rapid block finalization and the handling of large transaction volumes, all while maintaining a manageable number of active voting nodes.
Pros of DPoS consensus mechanism:
- High throughput: A smaller number of block producers leads to faster transaction processing, as fewer participants are involved in validation.
- Low finalization delays: Blocks are produced at fixed, predictable intervals, ensuring near-instantaneous finality.
Cons of DPoS:
- Centralization risks: Power is concentrated within a select group of delegates, which can lead to reduced decentralization and influence over the network.
- Censorship and trust risks: If block producers collude, they may censor transactions or undermine the integrity of the system, eroding trust in the network.
Liquid Proof-of-Stake (LPoS)
LPoS is a consensus model where token holders maintain full control over their coins, only transferring voting rights to validators. Stakeholders delegate their tokens to a chosen validator without giving up access to their funds. When a validator is selected to create a block, the total amount of staked tokens—including both the validator’s and those delegated to them—is considered. The validator receives a reward for the block and distributes a portion of it among the delegators based on their contribution. This model combines the economic incentives of Proof-of-Stake (PoS) with flexible risk management for token holders, offering both rewards and control.
Advantages of LPoS:
- Flexibility of participation: small holders can delegate their stake to validators without needing to operate their own node.
- Strong motivation for validators: the potential loss of delegated funds incentivizes validators to maintain the reliability and security of the network.
- Improved decentralization: by pooling small stakes, a broader and more diverse range of participants can be involved in the network’s governance and operation.
Cons of LPoS:
- Risk of power concentration: popular validators may attract a large portion of the total staked tokens, leading to centralization of power.
- Complexity of reward calculation: distributing rewards fairly among validators and delegators requires precise and transparent calculation.
- Delays in redistribution: shifting delegates or moving stakes between validators can take time, delaying potential reallocation of funds.
Examples of LPoS: Tezos (XTZ).
The Proof-of-Stake Evolution: Role of Hybrid Consensus Mechanisms
Hybrid consensus models combine the best features of PoW and PoS, addressing the major drawbacks of each—PoW’s high energy consumption and PoS’s centralization risk among large stake validators. Below, we explore examples of how these hybrid approaches are implemented in leading projects, as well as the evolution of PoS family protocols.
Decred:
- PoW consensus mechanism: Miners generate block candidates and receive rewards.
- PoS consensus mechanism: Token holders purchase “tickets” and vote on the inclusion of each block; ≥ 3 votes from 5 randomly selected tickets are required for finalization.
- Reward distribution: ~60% to miners, 30% to stakers, 10% to the development fund.
- Protection against 51% attacks: An attacker would need control over both > 50% of the hash rate and > 50% of the tickets, making such an attack economically infeasible.
Casper FFG (Ethereum)
- Initial model: A checkpoint finalization layer built on top of the PoW chain; every N blocks, validators vote on their finality.
- The Merge (September 2022): Ethereum transitioned to pure PoS with FFG finalization, disabling PoW mining.
- Further development: Researching Correct-by-Construction (CBC)—a PoS algorithm of blockchain that operates without a PoW layer.
Ouroboros (Cardano). A family of PoS protocols evolving over multiple versions:
- Classic: Deterministic leader selection based on stake.
- Praos: Introduces unpredictable sampling through VRF, providing resistance to synchronization attacks.
- Genesis: Eliminates trusted checkpoints, allowing new nodes to independently verify the entire history using PoS proofs.
BFT-based and Permissioned Solutions
BFT (Byzantine Fault Tolerance) protocols enable a group of validators to reach consensus on a single block, even in the presence of faulty or malicious participants. The process works as follows:
- A validator proposes a new block.
- The remaining validators verify the block and cast their votes as either “for” or “against.”
- Once the majority votes “for,” the block is added to the chain.
- Even if up to a third of the validators fail or act maliciously, the network remains intact and will not split.
Example: In the Tendermint protocol (used by the Cosmos network), validators take turns proposing blocks, rapidly exchange votes, and can handle hundreds of transactions per second, ensuring fast finality and robust security.
Private (permissioned) Networks
In this model, only pre-selected participants are allowed to vote:
- All nodes undergo verification (e.g., KYC and legal agreements).
- Validator composition is managed by a single operator or a consortium.
- Decision-making is fast due to a high level of trust between validators.
- Disadvantage: This structure often results in low decentralization and reliance on “club” rules, as decisions are made within a closed group.
Example: Hyperledger Fabric, used in corporate networks, where companies independently determine the composition of validators, ensuring controlled and trusted decision-making among a limited set of participants.
Proof-of-Authority (PoA)
PoA blockchain algorithmis a specialized form of consensus used in private networks where only “trusted” nodes are allowed to create blocks:
- Granting rights: The authority to propose blocks is granted by the network operator or a consortium of trusted participants.
- High performance: Block confirmation happens in fractions of a second, with throughput capable of handling thousands of transactions per second.
- Centralization and control: Since only some trusted nodes are involved, it’s crucial to have clear, transparent processes for appointing, replacing, and auditing these nodes.
Example: VeChain and Gnosis Chain (formerly xDai).
DAG and New Asynchronous Protocols
Modern blockchains are moving away from the rigid linear structure of blockchains and minimizing finalization delays. Directed Acyclic Graph (DAG) and asynchronous protocols, such as Avalanche, provide an alternative approach: transactions or nodes form a directed acyclic graph where there is no single “main branch,” and blockchain consensus is achieved through local confirmations and repeated voting.
- IOTA (Tangle): each node confirms the two previous transactions when creating a new one. There is no mining or fees, allowing for thousands of transactions per second (TPS). To protect against spam, IOTA temporarily uses a Coordinator, which will eventually be disabled through the Coordicide process;
- Hedera Hashgraph: the “gossip about gossip” mechanism in Hedera distributes both data and its history, followed by virtual voting on this history to achieve asynchronous Byzantine Fault Tolerance (BFT) finalization in a fraction of a second;
- Asynchronous voting over DAG In Avalanche-like protocols, consensus is achieved through a series of parallel, random polls:
- A node randomly polls a group of neighbors about a specific transaction.
- After receiving enough “yes” votes, the poll expands to a larger group of nodes.
- Once sufficient confidence is reached, the node finalizes the transaction with high (albeit probabilistic) certainty.
The subprotocols—Slush, Snowflake, Snowball, and Avalanche—provide confidence accumulation and resistance to BFT failures without a designated leader. TPS can reach tens of thousands, and finalization typically occurs in less than 1 second.
Subprotocols:
- Slush: The simplest form of voting.
- Snowflake: Introduces memory of prior responses.
- Snowball: Builds confidence in responses.
- Avalanche: Combines all previous mechanisms to ensure reliable finalization.
Advantages: The system offers tens of thousands of TPS, finalization in under 1 second, and resistance to Byzantine failures without a strict leader.
Consensus Mechanism Blockchain Comparison
Let’s look at a summary chart of key consensus algorithms.
| Blockchain consensus algorithm | Throughput | Energy efficiency | Examples |
| Proof-of-Work | 3–7 TPS | Low | Bitcoin, Litecoin |
| Proof-of-Stake (ETH) | ≈ 15 TPS | High | Ethereum |
| Proof-of-Stake (ADA) | ≈ 250 TPS | High | Cardano |
| Delegated PoS | ≈ 4 000 TPS | High | EOS, TRON |
| Liquid PoS | ≈ 60 TPS | High | Tezos |
| PBFT/PoA | ≈ 3 000 TPS | High | Hyperledger Fabric, PoA-сети |
| DAG (Hashgraph) | > 10 000 TPS | High | Hedera Hashgraph |
| DAG (IOTA — Tangle) | ≈ 1 000 TPS | High | IOTA (Tangle) |
| Avalanche Protocol | ≈ 4 500 TPS | High | Avalanche Network |
Experimental and Promising Algorithms
In addition to classic models, new and promising approaches to achieving consensus in blockchain are emerging:
- Proof-of-History (PoH): Utilizes verifiable delay functions (VDFs) to embed unique timestamps into the block stream, simplifying event ordering and transaction chronology verification. This approach is used in Solana.
- Proof-of-Importance (PoI): Validators are selected based not only on their stake size but also on their activity and interactions within the network. This encourages real economic participation and prevents the passive accumulation of power. NEM uses PoI.
- HotStuff: A simplified asynchronous BFT protocol with a single voting round, providing fast and predictable finality in large-scale networks. It is the consensus model used in Libra/Diem.
- PHANTOM/GHOSTDAG: An extended DAG model with parallel branches and block “clustering.” Transactions are finalized by analyzing the graph structure, enabling high throughput.
- Proof-of-Capacity (PoC): Validators are selected based on the amount of pre-allocated disk space; the probability of selection is proportional to the storage occupancy. Burstcoin is an example of PoC.
- Proof-of-Elapsed-Time (PoET): Each node starts a random timer in a secure environment (TEE), and the first timer to expire grants the right to create a block. This minimizes energy consumption while maintaining security, as seen in Intel Sawtooth.
List of cryptocurrencies by market capitalization
Conclusion
The consensus algorithm in blockchain is the foundation of blockchain networks, and the types of blockchain consensus are constantly evolving to address the increasing demands for scalability, attack resistance, and energy efficiency. While traditional PoW and PoS models remain central, they are now being enhanced by hybrid approaches, DAG architectures, and experimental protocols. The future of blockchain is not limited to current solutions—more innovative and groundbreaking advancements are on the horizon, driving the next phase of blockchain technology.